
Identifying Nefarious Telegram Users without the Help of Telegram Itself: Testing Solutions for Intelligence and Security Professionals in Fighting ISIS in the Encrypted Social Media Space
Introduction
Telegram currently is, for a plethora of reasons, the favorite encrypted social media app employed by ISIS.[1] As such, Telegram has become the subject of deep controversies in the West. While government officials demand for Telegram to store and hand over user information of those promoting terrorism, Telegram’s executives have responded with an adamant refusal to comply. This conundrum between governments wanting to balance security against encrypted social media executives arguing in behalf of the rights to free speech and surveillance-free communications—particularly in authoritarian regimes—has led researchers at ICSVE to question if it’s possible to assist law enforcement in identifying nefarious users on Telegram without demanding the assistance of the app itself. This article reports on our researchers’ successful attempts to test a few potential approaches that show promise.
Background
There is no doubt that ISIS has been the most successful tech-oriented terrorist organization in history that not only understands how to use the Internet for communication purposes but also has learned to do so while hiding their messaging and identities. ISIS cadres use the surface web, deep web, dark web, social media and encrypted messaging apps, such as Telegram, to disseminate their propaganda, recruit new members, inspire or even direct their followers to carry out terror attacks which all cause serious concerns for law enforcement, intelligence and security professionals tasked with staying one step ahead in fighting the group[2]. It bears noting that ISIS also surfaced at a time when social media’s feedback mechanisms were developed enough to allow ISIS to distribute their slick propaganda to global audiences and then hone in on those who show interest. By virtue of a retweet, like, or other endorsement of their products they are able to personally contact those who show interest.[3] In recent years Twitter, Facebook, YouTube and other web-based social media apps have cracked down on ISIS’s presence on their platforms making it harder to carry out intensive grooming and recruiting on these web-based apps. This however, resulted in ISIS using fleeting accounts on mainline web-based apps like Twitter, YouTube and Facebook to quickly attract the attention of those interested in their propaganda and then migrate potential recruits onto encrypted apps such as Telegram where they may then engage with them on a much more intensive level and for a longer time period without disruption—to motivate and direct some into carrying out actual attacks.
While we can monitor most of ISIS’ activity on the web-based Internet (i.e. YouTube, Facebook, Twitter, etc.) through web crawlers and search engines, law enforcement and intelligence agencies struggle when it comes to intercepting valuable intelligence that could support in preventing and disrupting terror attacks on messaging apps, such as Telegram that are encrypted and thus prevent such efforts.
In response to these very real security issues, Russia’s FSB (security service) announced on June 26 (2017) that terrorists had used Telegram to coordinate and plan a deadly suicide bombing on Russian soil by providing “terrorists with the opportunity to create secret chats rooms with a high degree of encryptionâ€[4]. As a result, Russian officials increased their pressure upon Telegram to provide security-related information to Russian security services. In response, Telegram’s founder, Pavel Durov, agreed for his firm to be registered in Russia, but insisted on not sharing any private data with the Russian government, stating that he does not want to undermine the privacy of the six million Russian Telegram users currently registered on the app.[5] Indeed, this is not a simple dilemma, as it pits the rights of free speech and surveillance-free communication in an authoritarian regime against the need for security concerns about potential terrorist attacks. This underlying problem of cooperation between counter-terrorism (CT) officials and any tech-company is what we call the “business-security†dilemma.
The “business-security†dilemma describes a situation, in which tech companies, such as social-media or encrypted messaging apps, have to choose between two options, each that have negative consequences for both parties. Companies that cooperate with law enforcement and intelligence agencies by providing access to private data hopefully address security threats from terrorism, but by doing so, demonstrate their failure to value and protect the privacy and free speech of its users—which is particularly harmful to encrypted social media apps which exist precisely for that purpose. Law enforcement and intelligence agencies also lose if tech-companies cooperate, as many users—both benign and nefarious—will stop using the app and download another. On the other hand, if the social media app executives do not cooperate, bad press inevitably follows, framing the company as a ‘terrorist supporter’. Thus, with either choice—compliance or refusal, the company faces negative consequences, from its customers or the security sector, as does the CT-community.
Social media companies, such as Facebook, Twitter and YouTube face a similar dilemma, costing them time and resources which do not directly support their products in efforts at surveillance and takedowns which may also turn away users. Their dilemma is less severe however, as their apps do not depend solely on being able to provide encrypted communications. In the case of these web-based, open source social media there are also web-crawlers and business applications that could be used by these companies to detect and take down a lot more ISIS content than is currently being taken down at present.[6] And, it should not be forgotten that social media companies are masters in collecting data on users for targeted advertising purposes. Perhaps for them, it would be advisable to use existing technology and modify it to identify violent extremist online propaganda?
Encrypted apps are another story and cannot be crawled in this manner. In either case, extremist content is spreading, versus decreasing, on social media and law enforcement simply can’t keep up while social media companies, for reasons unknown, have not yet opted to use available technologies for more comprehensive and speedy takedowns. As a result, we are failing in countering extremist content online. However, as a recent Guardian article argued: “Counter-terrorism was never meant to be Silicon Valley’s jobâ€.[7]
Moreover, due to growing concerns of consumers about hacking, as well as anxieties raised about government surveillance (particularly following Edward Snowden’s shocking revelations), a large number of mobile phone users have turned to encrypted messaging apps. In 2016, Telegram was downloaded 49,28 million times, followed by Wickr-Me with 3.8 million, Signal with 3.62 million, and other encrypted messaging combined with 0.35 million downloads[8]. When we look at these numbers, we have to ask ourselves, if our citizens value privacy more than they value security from terrorist threats? Do the costs of losing privacy, free speech and surveillance-free communications outweigh the benefits? Indeed, the number of terrorists compared to the vast majority of Telegram (and other encrypted app) users who are benign and have no intention to commit an act of terror is very low. If all Telegram users were in fact terrorists, we should see terror attacks every single day. But, fortunately, we don’t.
Nevertheless, we should not give up on chasing terrorists and shutting down their activities in the encrypted space; but instead of demanding the encrypted apps cooperate with government, it may be more useful to independently develop creative methodologies to gain valuable intelligence on those individuals engaging with and distributing ISIS propaganda as well as recruiting and directing terrorist attacks. In particular, with ISIS relying so heavily on Telegram, we need at present to find ways to fight ISIS without demanding any help of Telegram, whose executive leadership refuses in any case, to release encrypted information needed to fight jihadists using their messaging app. [9]
Identifying Nefarious Telegram Users without the Help of Telegram
So, how can we deal with this very tiny fraction of Telegram users who support and share ISIS content? To this end, we were interested in two questions: first, can we learn if pro-ISIS Telegram users employ information security (InfoSec) measures, such as virtual private networks (VPNs), to protect their identity and if not, are they identifiable? Second, is it possible to identify ISIS endorsing Telegram users communicating via private messaging without any help from Telegram, to make it possible for the law enforcement or intelligence community to do the same?
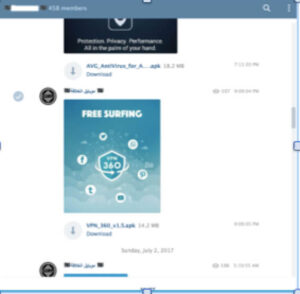
ISIS, as well as other militant jihadi groups have long been concerned with promoting information security to their members to enable them to evade law enforcement and intelligence. Among the many InfoSec groups ISIS promotes to their members, one known as “Horizon†has published manuals in multiple languages on topics like VPNs, secure browsers and the deep and dark web. In 2015, researchers discovered that ISIS had been using a 34-page operational manual that demonstrates just how tech-savvy ISIS really is. This manual was written in 2014 by a Kuwaiti cyber-security firm for journalists and activists in Gaza, but it was also found in ISIS chat rooms. Topics that are covered range from how to use Twitter, with a focus on protecting identity, to using encrypted Internet browsers and keeping telecommunications private.[10] At ICSVE, our researchers have been monitoring pro-ISIS Telegram channels for quite a while and we have also come across several Telegram channels that serve solely one purpose, namely educating pro-ISIS individuals in information security. Fig.1 shows a screenshot of a pro-ISIS channel that shares free tools, such as anti-virus software or VPN tools on a daily basis. According to Alkhouri, “such advice is what helped many jihadists bypass scrutiny and operate online with easeâ€.[11]
 Given the dissemination of these manuals and ISIS’ intent of educating its followers about the importance of information security, we were keen to test if Telegram users operating in ISIS space actually are actually savvy enough to have implemented these InfoSec measures or if they fail to pay attention. To this end, we conducted a small experiment on Telegram, which was comprised of two approaches. Concerning our methodology, we have decided not to reveal it here as it was used to learn the identities of pro-ISIS Telegram users and we do not wish to further educate them in terms of information security. In this respect, it must be highlighted that this
Given the dissemination of these manuals and ISIS’ intent of educating its followers about the importance of information security, we were keen to test if Telegram users operating in ISIS space actually are actually savvy enough to have implemented these InfoSec measures or if they fail to pay attention. To this end, we conducted a small experiment on Telegram, which was comprised of two approaches. Concerning our methodology, we have decided not to reveal it here as it was used to learn the identities of pro-ISIS Telegram users and we do not wish to further educate them in terms of information security. In this respect, it must be highlighted that this
Figure 1: Pro-ISIS Telegram User sharing VPN and Anti-Virus Apps
methodology should not be perceived as a ‘silver-bullet’, but more as a ‘cause for thought’ to develop better and more effective approaches. At ICSVE, we strongly believe that any effort to fight ISIS on the digital battleground is better than doing nothing—particularly as ISIS loses territory and increasingly promotes and directs homegrown attacks via the Internet.
The first approach was OSINT-informed and had the objective to identify the social media accounts of pro-ISIS Telegram users that in turn provides us with valuable intelligence about the actual identity of the person and his or her wider network. By employing our techniques, we were able to gain the actual identities of 3 users in a private chatroom, however, we will only highlight one case herein as the method is the same. In this regard, it is also necessary to emphasize that corroborating our results was one of the main challenges of this approach, however, after analyzing the whole case, we were quite confident in our judgements as the evidence was overwhelming.
 In the first approach, we focused on private chat rooms as they allow us (not always) to see the actual group members in terms of numbers and profiles (Fig.3). In this case, we explored a private chat room, which primarily disseminates official ISIS propaganda (Fig.2).
In the first approach, we focused on private chat rooms as they allow us (not always) to see the actual group members in terms of numbers and profiles (Fig.3). In this case, we explored a private chat room, which primarily disseminates official ISIS propaganda (Fig.2).
Figure 2: Pro-ISIS Private Chatroom

In this case, a profile (see Fig. 3 – highlighted in red) caught our eyes for several reasons (that we don’t explain here as it would reveal our methods). We were keen tofind one of the target’s social media accounts which might revel his or her real identity. Generally, we assumed, that even though individuals employ encrypted-messaging apps for privacy for their terrorist-enga
ging purposes, they still have active social media social media accounts registered in their own real identities. And, in this particular case, we were right).
Figure 3: Members of the private chatroom (Telegram)
In fact, we were quite surprised how easy it was to identify this particular Telegram user. However, it should be mentioned that this approach does not work with any Telegram user, but it is definitely worth a try for the purpose of gaining valuable intelligence (see Fig.4).

Â
Figure 4: Facebook Profile of Telegram User
A quick scan of the pictures (see Fig. 5), which were posted on this individual’s Facebook account, reveals more about the individual. Especially the knife picture (highlighted in red) caught immediately our attention, as in Telegram the same individual was endorsing and sharing violent ISIS propaganda material that causes us to view him as radicalized and potentially considering engaging in violence. To learn if his knife picture was unique to him we searched the same image on the surface web and found out that this picture was posted repeatedly on other websites. In other words, the individual simply copied and pasted the picture, which also implies that the target is most probably not in possession of that particular knife. Yet his Telegram activity makes clear he may be considering enacting violence. To be on the safe side we passed our information, including his identity, on to the relevant security authorities for them to determine whether or not he constitutes an actual terrorist threat.
other websites. In other words, the individual simply copied and pasted the picture, which also implies that the target is most probably not in possession of that particular knife. Yet his Telegram activity makes clear he may be considering enacting violence. To be on the safe side we passed our information, including his identity, on to the relevant security authorities for them to determine whether or not he constitutes an actual terrorist threat.
Figure 5: Pictures posted by the individual on Facebook
Our second approach tested whether or not pro-ISIS Telegram users employ information security measures, such as VPNs or a Proxy, to disguise their IP-addresses. We need to emphasize that we were also aware of the fact that individuals could use a Tor browser, public Wi-Fi or similar tools. In these cases, we would not be able to know if the IP address ties to that individual or not. Likewise, we were aware of the fact that identifying someone’s IP address would not give us his or her real name, exact location, or anything like that. In general, we assumed that most individuals use Telegram on a daily basis, meaning that whenever they have time to check out the latest posts, they would use their mobile phones to have a quick look. Furthermore, we assumed that these individuals would probably not use a VPN or Proxy every single time they access Telegram, even if installed, because it often slows down the Internet speed and individuals may just forget about activating the VPN when anxious to view new posts.
With all these assumptions in mind, we again went back to one of the private chat rooms to carry out a small experiment (see Fig. 6). Our experiment  was exploratory in nature as we haven’t come across a similar approach in the  literature or on the Internet, however, we are aware that many intelligence agencies have been using the same or similar techniques. Overall, we needed four attempts to gather a sample of three out of all of the 138 group members that we then studied for their use of a VPN or Proxy. From these three individuals, two have not used a VPN or Proxy as in contrast to the third individual who used a Proxy Server (located in Cyprus). In this respect, it is paramount to highlight that these results should be interpreted carefully as the method used is not 100% accurate. Furthermore, those two individuals identified could have also used a Tor Browser or public Wi-Fi, for example. So, how reliable is the method then?
was exploratory in nature as we haven’t come across a similar approach in the  literature or on the Internet, however, we are aware that many intelligence agencies have been using the same or similar techniques. Overall, we needed four attempts to gather a sample of three out of all of the 138 group members that we then studied for their use of a VPN or Proxy. From these three individuals, two have not used a VPN or Proxy as in contrast to the third individual who used a Proxy Server (located in Cyprus). In this respect, it is paramount to highlight that these results should be interpreted carefully as the method used is not 100% accurate. Furthermore, those two individuals identified could have also used a Tor Browser or public Wi-Fi, for example. So, how reliable is the method then?
Figure 6: Private Pro-ISIS Telegram ChatroomÂ
To be on the safe side, we have also used the same method to disguise the IP addresses of friends who use Telegram on a daily basis. We conducted this experiment in three rounds. Round one gave instructions on using a VPN or Proxy. Round two gave instructions on not using any of the InfoSec measures. Round three tested our method in the “Secret Chat†that uses end-to-end encryption, leaves no traces on Telegram servers, has a self-destruct timer and does not allow forwarding, by telling our friends not to use a VPN or Proxy. Overall, we were successful in disguising the IP-addresses (Round 2 and 3) and most importantly, to detect the Proxy or VPN (Round 1). With this in mind, we were confident that our results with the small pro-ISIS sample was similarly successful.
Conclusion
ICSVE’s brief exploratory incursions on Telegram tell us two things. One that it is possible to penetrate ISIS Telegram chat rooms and inside them find the social media accounts, and thus identities, of those who appear to be serious ISIS devotees. Likewise of these we were able to find, we learned that some do not take the precautions of using a VPN or Proxy network, despite ISIS’s instructions to do so. Most surprisingly, we found out that our method even works in the Secret Chat, a special service that makes Telegram so famous for being secure. Our small experiments should be seen as an attempt of exploring and discovering creative ways to identify pro-ISIS Telegram users. Most importantly, we want to demonstrate that there are ways to fight ISIS in encrypted messaging apps, even though Telegram itself is refusing to cooperate.
There is also still the matter of social media giants such as Facebook, YouTube and Twitter using available technologies to take ISIS content and accounts down faster so that there is not the opportunity to engage and be seduced off the open source web-based social media into the encrypted social media apps that are harder to track. However our short experiment demonstrates that tracking is possible even when not having Telegram’s cooperation. And this was just the beginning.
Note to readers: Our expertise and methodology is freely available to law enforcement and intelligence agencies upon request.
Reference for this article: Lorand Bodo, M.A. & Anne Speckhard, Ph.D. (July 15, 2017) Identifying Nefarious Telegram Users without the Help of Telegram Itself: Testing Solutions for Intelligence and Security Professionals in Fighting ISIS in the Encrypted Social Media Space. ICSVE Research Reports. https://www.icsve.org/research-reports/identifying-nefarious-telegram-users-without-the-help-of-telegram-itself-testing-solutions-for-intelligence-and-security-professionals-in-fighting-isis-in-the-encrypted-social-media-space/
About the authors:
Lorand Bodo is a Research Fellow at ICSVE. Â For his PhD, Lorand wants to develop an evidence-based risk assessment protocol for terrorists in Europe. At ICSVE, Lorand is testing the effectiveness of ISIS defector counter-narrative videos with those who endorse ISIS on the internet. In a similar vein, he tries to develop methodologies to identify these users by using OSINT and SOCMINT. Lorand Bodo graduated with distinction in Governance and International Politics (MA) from Aston University and is about to finish his second MA degree in Politics with a focus on the Governance of Complex Innovative Technological Systems from the University of Bamberg.
Anne Speckhard, Ph.D. is Adjunct Associate Professor of Psychiatry at Georgetown University in the School of Medicine and Director of the International Center for the Study of Violent Extremism (ICSVE) where she heads the Breaking the ISIS Brand—ISIS Defectors Interviews Project. She is the author of: Talking to Terrorists, Bride of ISIS and coauthor of ISIS Defectors: Inside Stories of the Terrorist Caliphate; Undercover Jihadi; and Warrior Princess. Dr. Speckhard has interviewed nearly 500 terrorists, their family members and supporters in various parts of the world including Gaza, West Bank, Chechnya, Iraq, Jordan, Turkey and many countries in Europe. In 2007, she was responsible for designing the psychological and Islamic challenge aspects of the Detainee Rehabilitation Program in Iraq to be applied to 20,000 + detainees and 800 juveniles. She is a sought after counterterrorism experts and has consulted to NATO, OSCE, foreign governments and to the U.S. Senate & House, Departments of State, Defense, Justice, Homeland Security, Health & Human Services, CIA and FBI and CNN, BBC, NPR, Fox News, MSNBC, CTV, and in Time, The New York Times, The Washington Post, London Times and many other publications. Her publications are found here: https://georgetown.academia.edu/AnneSpeckhardWebsite: https://www.icsve.org
[1] Yayla, Ahmet S and Speckhard, Anne (2017). Telegram: The Mighty Application that ISIS Loves, available at: https://www.icsve.org/brief-reports/telegram-the-mighty-application-that-isis-loves/ (29.06.2017)
[2] Callimachi, R. (2017). Not ‘Lone Wolves’ After All: How ISIS Guides World’s Terror Plots From Afar, available at: https://www.nytimes.com/2017/02/04/world/asia/isis-messaging-app-terror-plot.html (29.06.2017).
[3] Speckhard, A., Shajkovci, A. & Yayla, A. S. (2016). “Defeating ISIS on the Battle Ground as well as in the Online Battle Space: Considerations of the “New Normal†and Available Weapons in the Struggle Aheadâ€. Journal of Strategic Security 9, no.4, p.1-10.
[4] Reuters (2017). Russia, Upping Pressure on Telegram App, Says It Was Used to Plot Bombing, available at: https://www.nytimes.com/reuters/2017/06/26/technology/26reuters-russia-telegram-security.html (29.06.2017).
[5] Reuters (2017). Telegram App Agrees to Register in Russia, but Not to Share Private Data, available at: https://www.nytimes.com/reuters/2017/06/28/technology/28reuters-russia-telegram-security.html (29.06.2017).
[6] See for example: GIPEC (2017). Who we are: GIPEC, available at: http://www.gipec.com/who-we-are/ (30.06.2017).
[7] Solon, O. (2017). Counter-terrorism was never meant to be Silicon Valley’s job. Is that why it’s failing? available at: https://www.theguardian.com/technology/2017/jun/29/silicon-valley-counter-terrorism-facebook-twitter-youtube-google (29.06.2017).
[8] Roberts, J. J. (2017) Here Are the Most Popular Apps for Secure Messages, available at: http://fortune.com/2017/01/17/most-popular-secure-apps/ (29.06.2017).
[9] The Times (2017). Message app used by Isis refuses to fight jihadists, available at: https://www.thetimes.co.uk/article/message-app-used-by-isis-refuses-to-fight-jihadists-jrddv7c93 (30.06.2017)
[10] Murgia, M. (2015). Islamic State uses detailed security manual, revealing its cyber strategy, available at: http://www.telegraph.co.uk/technology/internet-security/12007170/Islamic-States-detailed-security-manual-reveals-its-cyber-strategy.html (29.06.2017). (You can also find the manual here)
[11] Alkhouri, L. (2017). How Cyber-Jihadists Protect Their Identities and Their Posts, available at: https://www.thecipherbrief.com/column/private-sector/how-cyber-jihadists-protect-their-identities-and-their-posts-1092 (29.06.2017).
